Security
The Cyber Defense Benchmark: Why Every Frontier LLM Failed
We ran Claude, GPT-5, Gemini, and 8 other frontier LLMs through 884 agentic threat-hunting runs on real attack telemetry. The headline result: zero passed.
Simbian Research Lab
April 28, 2026
Security
What Really Happens During an AI-Armed Attack
Discover what really happens during an AI-armed cyberattack. Learn how generative AI uses contextual phishing, mutant malware, and entropy bombs to bypass SOCs.
Alankrit Chona
April 20, 2026
Security
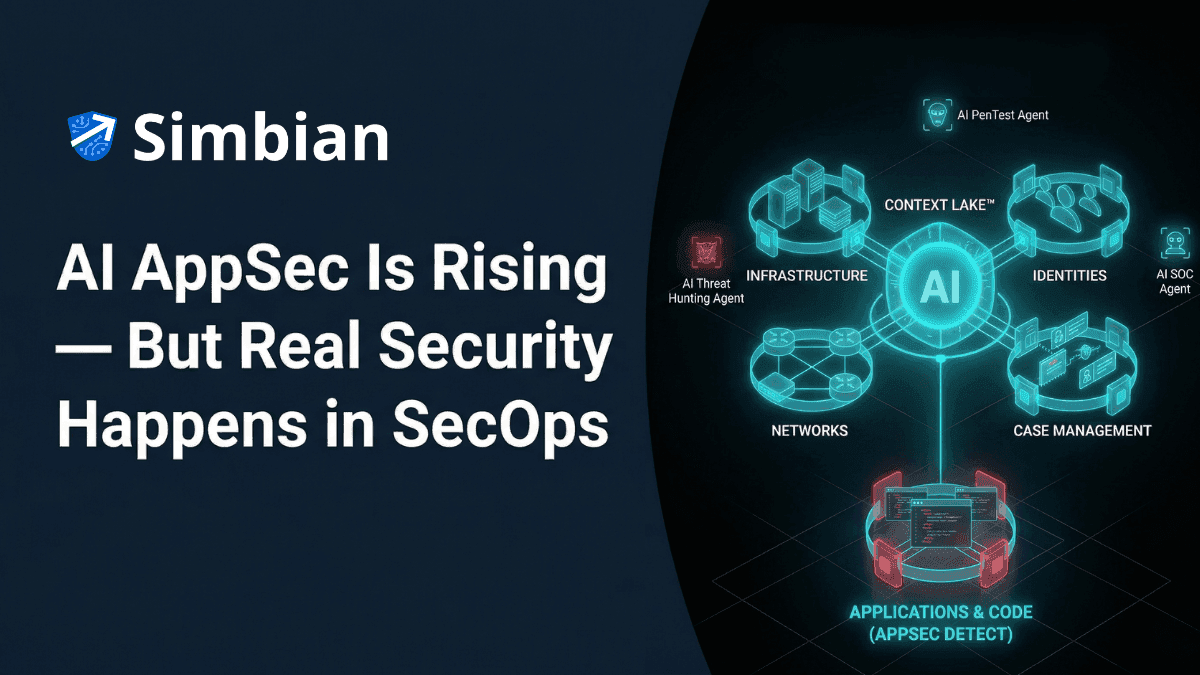
AI AppSec vs AI SecOps: Why Real Security Requires an AI SecOps Platform
AI AppSec tools secure code. Real risk lives in security operations. See why AI-native SecOps platforms with Context Lake beat standalone AI AppSec tooling for enterprise security teams.
Igor Kozlov
March 26, 2026
Security
SOAR Alternatives: Why Your AI SOAR is not AI SOC
100+ playbooks. 40% alerts uninvestigated. AI features on SOAR don't fix broken architecture. Learn why AI SOC replaces SOAR reasoning — not just its UI — and how to migrate without disruption.
Sumedh Barde
February 18, 2026
Security
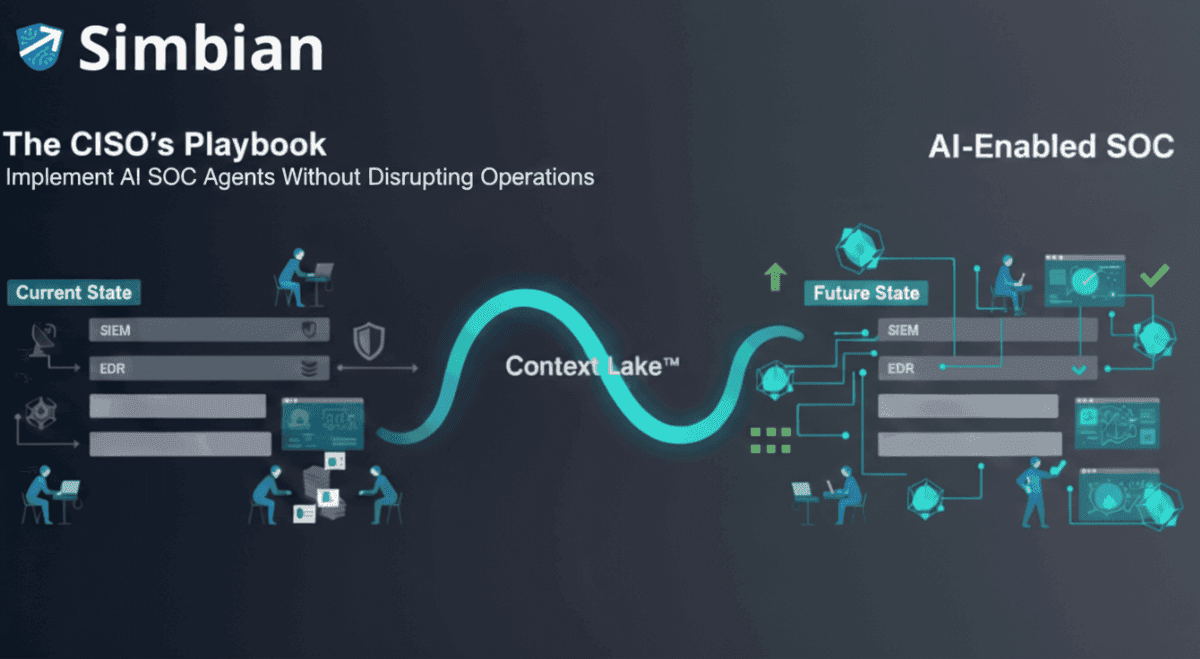
The CISO's Playbook: How to Implement AI SOC Agents Without Disrupting Your Security Operations
Step-by-step guide for CISOs implementing AI SOC agents in 2026. Learn what changes, what stays, and how to achieve 90%+ auto-resolution without disrupting operations.
Ambuj Kumar
January 13, 2026

Security
How to Lose an AI Gunfight: Bring a Knife and Asset-Centric Security
In an era where AI has supercharged cyber-offense, asset-centric security is no longer enough. This post explores why a shift to an attacker's perspective is critical for survival, detailing the four pillars of modern offensive security: penetration testing, red teaming, attack surface management (ASM), and breach & attack simulation (BAS). Learn why traditional, compliance-driven security is falling behind and how to adapt to the new speed of cyber threats.
Sumedh Barde
November 17, 2025
Security
Anthropic's AI Espionage Report: Why AI SOC Is Critical for Defense
An AI spy just infiltrated 30 global targets. Here's why your SOC needs AI defense and how Simbian responds to the threat.
Igor Kozlov
November 14, 2025

Security
AI-Accelerated Threat Hunts for Microsoft 365 and Sentinel
Discover how Simbian’s AI Threat Hunt Agent accelerates Microsoft 365 & Sentinel hunts with automation, deeper insights, and autonomous hypothesis validation.
Sumedh Barde
September 30, 2025
Security
AI for Cybersecurity: Solving Alert Overload with AI SOC Solutions
Discover how AI transforms cybersecurity by reducing alert fatigue in SOC operations. Learn about AI SOC analysts, automated threat detection, and overcoming alert overload with intelligent security automation.
Shivang Kalsi
September 9, 2025
Page 1 of 4
...
